
Belajar Kubernetes - Pengenalan dan Penjelasan Kubernetes Dashboard
Di episode ini kita akan coba bahas Kubernetes Dashboard untuk managing cluster melalui web UI. Kita akan mempelajari cara install Dashboard v2.7.0, create admin user, access dashboard, dan best practice untuk secure dashboard deployment.

#Pendahuluan
Di episode sebelumnya kita sudah belajar tentang StatefulSet untuk managing stateful application dengan stable identity dan persistent storage. Selanjutnya di episode 28 kali ini, kita akan coba bahas Kubernetes Dashboard, web-based UI untuk managing dan monitoring Kubernetes cluster kalian.
Catatan: Disini saya akan menggunakan Kubernetes Cluster yang di install melalui K3s.
Sementara kubectl powerful untuk command-line management, Kubernetes Dashboard menyediakan visual interface untuk viewing cluster resource, deploying application, troubleshooting issue, dan monitoring workload - making cluster management lebih accessible.
#Apa Itu Kubernetes Dashboard?
Kubernetes Dashboard adalah general-purpose, web-based UI untuk Kubernetes cluster. Dia allow user untuk manage application running di cluster, troubleshoot application, dan manage cluster resource.
Bayangkan Dashboard seperti control panel untuk cluster kalian - instead of typing command, kalian bisa click through resource, view log, edit configuration, dan monitor health melalui intuitive interface.
Fitur kunci Kubernetes Dashboard:
- Resource visualization - View semua cluster resource di satu tempat
- Application deployment - Deploy containerized application via UI
- Troubleshooting - View log, event, dan resource status
- Resource management - Create, edit, delete resource
- Monitoring - View CPU/memory usage dan metric
- RBAC integration - Respect Kubernetes permission
- Multi-namespace - Switch between namespace easily
- Real-time update - Live view cluster state
#Kenapa Gunakan Kubernetes Dashboard?
Dashboard solve beberapa challenge:
- Visual management - Lebih mudah daripada memorize kubectl command
- Quick troubleshooting - View log dan event di satu tempat
- Team accessibility - Non-CLI user bisa manage cluster
- Resource discovery - Browse semua resource visually
- Rapid deployment - Deploy app tanpa writing YAML
- Monitoring - Quick overview cluster health
- Learning tool - Understand Kubernetes structure visually
- Audit trail - See what's running di cluster kalian
Tanpa Dashboard, kalian rely entirely on kubectl, yang bisa challenging untuk beginner atau team preferring visual interface.
#Instalasi Kubernetes Dashboard v2.7.0
Mari kita install Dashboard v2.7.0 step by step.
#Step 1: Deploy Dashboard
Apply official Dashboard manifest:
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.7.0/aio/deploy/recommended.yamlIni create:
- Namespace:
kubernetes-dashboard - ServiceAccount, Secret, ConfigMap
- Deployment:
kubernetes-dashboard - Service:
kubernetes-dashboard - RBAC role dan binding
#Step 2: Verify Installation
Check Dashboard pod:
kubectl get pods -n kubernetes-dashboardOutput:
NAME READY STATUS RESTARTS AGE
dashboard-metrics-scraper-5cb4f4bb9c-xxxxx 1/1 Running 0 1m
kubernetes-dashboard-79cbcf9fb6-xxxxx 1/1 Running 0 1mCheck Dashboard service:
kubectl get svc -n kubernetes-dashboardOutput:
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.43.xxx.xxx <none> 8000/TCP 1m
kubernetes-dashboard ClusterIP 10.43.xxx.xxx <none> 443/TCP 1m#Step 3: Create Admin User
Dashboard require authentication. Create ServiceAccount dengan admin privilege.
Create dashboard-admin.yml:
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user
namespace: kubernetes-dashboard
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: admin-user
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: admin-user
namespace: kubernetes-dashboardApply configuration:
kubectl apply -f dashboard-admin.ymlWarning
Security Warning: Ini create user dengan cluster-admin privilege. Untuk production, gunakan more restrictive RBAC role.
#Step 4: Generate Access Token
Create token untuk admin user:
kubectl -n kubernetes-dashboard create token admin-userOutput (contoh):
eyJhbGciOiJSUzI1NiIsImtpZCI6IjRxN3Z...very-long-token...xyz123Copy token ini - kalian akan need it untuk log in ke Dashboard.
Catatan
Token created dengan create token adalah short-lived (default 1 jam). Untuk long-lived token, create Secret manually.
#Step 5: Access Dashboard
Ada beberapa cara untuk access Dashboard:
#Option 1: kubectl port-forward (Recommended untuk Development)
Forward Dashboard service ke localhost:
kubectl -n kubernetes-dashboard port-forward svc/kubernetes-dashboard 8443:443Access Dashboard di: https://localhost:8443
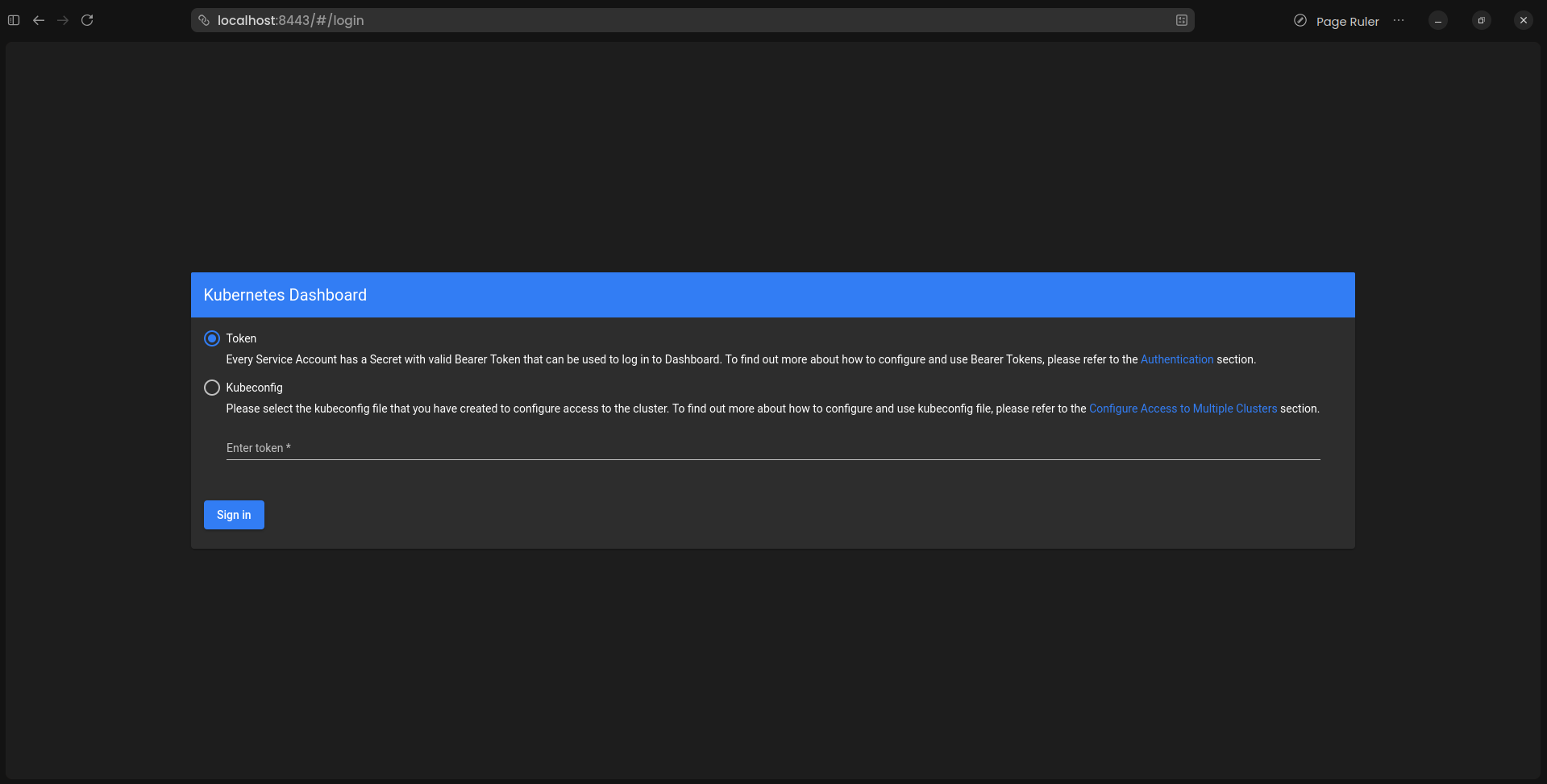 Kubernetes Dashboard Login
Kubernetes Dashboard Login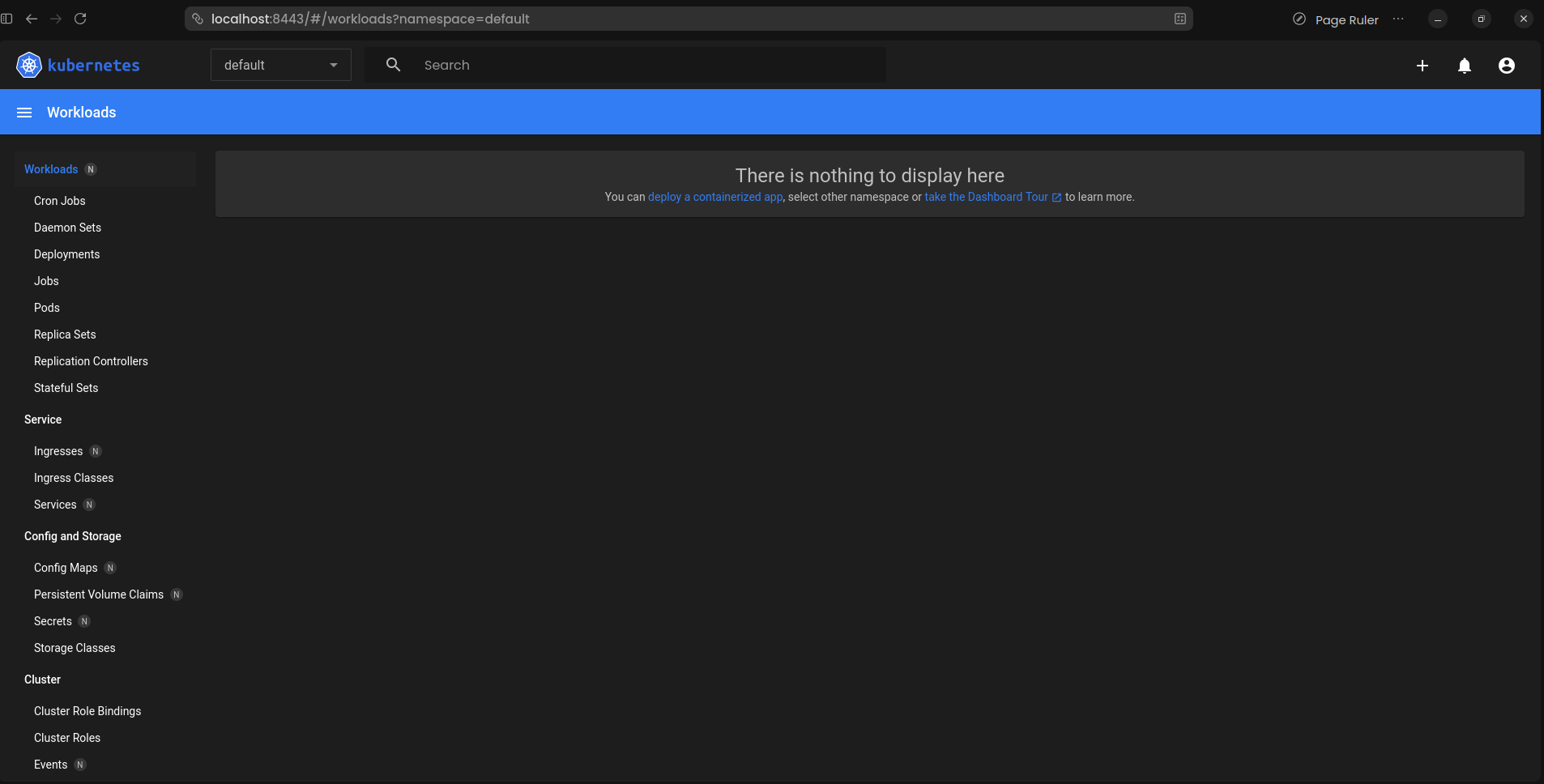 Kubernetes Dashboard Workload
Kubernetes Dashboard Workload#Option 2: Edit Service ke NodePort
Edit Dashboard service:
kubectl edit svc kubernetes-dashboard -n kubernetes-dashboardChange type: ClusterIP ke type: NodePort:
spec:
type: NodePort # Changed dari ClusterIP
ports:
- port: 443
targetPort: 8443
nodePort: 30443 # Optional: specify portGet NodePort:
kubectl get svc -n kubernetes-dashboardAccess Dashboard di: https://<node-ip>:<node-port>
#Option 3: Ingress (Recommended untuk Production)
Create Ingress resource:
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: kubernetes-dashboard
namespace: kubernetes-dashboard
annotations:
nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"
nginx.ingress.kubernetes.io/ssl-redirect: "true"
spec:
ingressClassName: nginx
tls:
- hosts:
- dashboard.example.com
secretName: dashboard-tls
rules:
- host: dashboard.example.com
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: kubernetes-dashboard
port:
number: 443#Step 6: Login ke Dashboard
- Open Dashboard URL di browser
- Kalian akan see certificate warning (self-signed cert) - accept it
- Select "Token" authentication method
- Paste token dari Step 4
- Click "Sign in"
Kalian sekarang logged in ke Kubernetes Dashboard!
#Dashboard Overview
#Main Section
Cluster:
- Node - View cluster node
- Namespace - Browse namespace
- Persistent Volume - Manage storage
- Role - View RBAC role
- Storage Class - View storage class
Workload:
- Deployment - Manage deployment
- Pod - View dan manage pod
- ReplicaSet - View replica set
- StatefulSet - Manage stateful app
- DaemonSet - View daemon set
- Job - View job
- CronJob - Manage scheduled job
Service:
- Service - View service
- Ingress - Manage ingress rule
- Network Policy - View network policy
Config and Storage:
- ConfigMap - Manage configuration
- Secret - View secret (value hidden)
- PersistentVolumeClaim - Manage PVC
Custom Resource:
- Custom Resource Definition - View CRD
#Menggunakan Dashboard
#Viewing Resource
Navigate ke any resource type:
- Click on resource type di sidebar (e.g., "Pods")
- Select namespace dari dropdown
- View list resource
- Click resource name untuk detail
#Viewing Pod Detail
- Navigate ke Workload → Pod
- Click pod name
- View:
- Pod status dan condition
- Container information
- Event
- Log (click "Logs" button)
- YAML definition
#Viewing Log
- Navigate ke pod detail
- Click "Logs" icon
- Select container (jika multi-container)
- View real-time log
- Gunakan search dan download feature
#Deploying Application
- Click "+" icon (top right)
- Choose method:
- Create from input (paste YAML)
- Create from file (upload YAML)
- Create from form (fill field)
- Enter configuration
- Click "Deploy"
Contoh form deployment:
App name: nginx-app
Container image: nginx:1.25
Number of pods: 3
Service: External (NodePort)
Port: 80
Target port: 80#Editing Resource
- Navigate ke resource
- Click resource name
- Click "Edit" icon (pencil)
- Modify YAML
- Click "Update"
#Deleting Resource
- Navigate ke resource
- Check checkbox next to resource
- Click "Delete" icon (trash)
- Confirm deletion
#Scaling Deployment
- Navigate ke Deployment
- Click deployment name
- Click "Scale" icon
- Enter desired replica
- Click "Scale"
#Executing Command di Pod
- Navigate ke pod detail
- Click "Exec" icon (terminal)
- Select container
- Execute command di shell
#Membuat Long-Lived Token
Untuk persistent access, create Secret-based token.
#Create Secret untuk ServiceAccount
apiVersion: v1
kind: Secret
metadata:
name: admin-user-token
namespace: kubernetes-dashboard
annotations:
kubernetes.io/service-account.name: admin-user
type: kubernetes.io/service-account-tokenApply:
kubectl apply -f admin-user-secret.yml#Get Token dari Secret
kubectl get secret admin-user-token -n kubernetes-dashboard -o jsonpath="{.data.token}" | base64 --decodeToken ini tidak expire dan bisa used untuk long-term access.
#Membuat Read-Only User
Untuk user yang should only view resource:
apiVersion: v1
kind: ServiceAccount
metadata:
name: readonly-user
namespace: kubernetes-dashboard
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: readonly-user
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: view
subjects:
- kind: ServiceAccount
name: readonly-user
namespace: kubernetes-dashboardApply:
kubectl apply -f dashboard-readonly.ymlGenerate token:
kubectl -n kubernetes-dashboard create token readonly-user#Membuat Namespace-Specific User
Untuk user limited ke specific namespace:
apiVersion: v1
kind: ServiceAccount
metadata:
name: dev-user
namespace: kubernetes-dashboard
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: dev-user
namespace: development
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: edit
subjects:
- kind: ServiceAccount
name: dev-user
namespace: kubernetes-dashboardUser ini hanya bisa access development namespace.
#Troubleshooting Dashboard
#Dashboard Pod Not Running
Check pod status:
kubectl get pods -n kubernetes-dashboardView pod log:
kubectl logs -n kubernetes-dashboard deployment/kubernetes-dashboardDescribe pod:
kubectl describe pod -n kubernetes-dashboard <pod-name>#Cannot Access Dashboard
Check service:
kubectl get svc -n kubernetes-dashboard
kubectl describe svc kubernetes-dashboard -n kubernetes-dashboardVerify port-forward running:
kubectl -n kubernetes-dashboard port-forward svc/kubernetes-dashboard 8443:443#Token Authentication Failed
Verify ServiceAccount exist:
kubectl get sa admin-user -n kubernetes-dashboardVerify ClusterRoleBinding:
kubectl get clusterrolebinding admin-userGenerate new token:
kubectl -n kubernetes-dashboard create token admin-user#Certificate Error
Dashboard gunakan self-signed certificate by default. Untuk production:
- Create proper TLS certificate
- Create Secret dengan certificate
- Update Dashboard deployment untuk use certificate
apiVersion: v1
kind: Secret
metadata:
name: kubernetes-dashboard-certs
namespace: kubernetes-dashboard
type: kubernetes.io/tls
data:
tls.crt: <base64-encoded-cert>
tls.key: <base64-encoded-key>#Kesalahan Umum dan Pitfall
#Kesalahan 1: Menggunakan cluster-admin untuk Semua User
Problem: Giving everyone full cluster access.
Solusi: Create role-specific user:
# Read-only user
roleRef:
kind: ClusterRole
name: view
# Edit user (no delete)
roleRef:
kind: ClusterRole
name: edit#Kesalahan 2: Expose Dashboard Publicly Tanpa Authentication
Problem: Dashboard accessible dari internet tanpa proper security.
Solusi: Gunakan salah satu approach ini:
- Keep Dashboard internal-only
- Gunakan VPN untuk access
- Implement additional authentication (OAuth2 proxy)
- Gunakan Ingress dengan authentication
#Kesalahan 3: Tidak Set Resource Limit
Problem: Dashboard pod bisa consume unlimited resource.
Solusi: Edit deployment untuk add limit:
kubectl edit deployment kubernetes-dashboard -n kubernetes-dashboardAdd:
resources:
requests:
memory: "128Mi"
cpu: "100m"
limits:
memory: "256Mi"
cpu: "200m"#Kesalahan 4: Menggunakan Short-Lived Token di Automation
Problem: Token expire setelah 1 jam.
Solusi: Create Secret-based token untuk automation:
apiVersion: v1
kind: Secret
metadata:
name: admin-user-token
annotations:
kubernetes.io/service-account.name: admin-user
type: kubernetes.io/service-account-token#Kesalahan 5: Tidak Monitor Dashboard Access
Problem: No audit trail Dashboard usage.
Solusi: Enable audit logging di Kubernetes API server dan monitor Dashboard access pattern.
#Best Practice
#Secure Access
Gunakan strong authentication:
# Minimum privilege principle
roleRef:
kind: ClusterRole
name: view # Not cluster-admin#Gunakan Ingress dengan TLS
Secure Dashboard dengan proper certificate:
spec:
tls:
- hosts:
- dashboard.example.com
secretName: dashboard-tls-cert#Implement Network Policy
Restrict Dashboard network access:
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: dashboard-access
namespace: kubernetes-dashboard
spec:
podSelector:
matchLabels:
k8s-app: kubernetes-dashboard
policyTypes:
- Ingress
ingress:
- from:
- namespaceSelector:
matchLabels:
name: ingress-nginx
ports:
- protocol: TCP
port: 8443#Set Resource Limit
Prevent resource exhaustion:
resources:
requests:
memory: "128Mi"
cpu: "100m"
limits:
memory: "256Mi"
cpu: "200m"#Gunakan RBAC Properly
Create role-specific user:
# Admin user - full access
# Developer user - namespace-specific
# Viewer user - read-only#Regular Token Rotation
Rotate token periodically:
# Delete old token
kubectl delete secret admin-user-token -n kubernetes-dashboard
# Create new token
kubectl apply -f admin-user-secret.yml#Monitor Dashboard Usage
Track who access Dashboard dan what they do:
kubectl logs -n kubernetes-dashboard deployment/kubernetes-dashboard#Keep Dashboard Updated
Regularly update ke latest version:
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.7.0/aio/deploy/recommended.yaml#Dashboard Alternative
Sementara Dashboard official, consider alternative:
Lens:
- Desktop application
- Multi-cluster management
- Built-in terminal
- Prometheus integration
K9s:
- Terminal-based UI
- Keyboard-driven
- Real-time update
- Resource management
Octant:
- Local web UI
- Plugin system
- Resource visualization
- Developer-focused
Rancher:
- Full platform
- Multi-cluster
- CI/CD integration
- User management
#Melihat Detail Dashboard
#Get Dashboard Resource
kubectl get all -n kubernetes-dashboard#Check Dashboard Version
kubectl get deployment kubernetes-dashboard -n kubernetes-dashboard -o jsonpath="{.spec.template.spec.containers[0].image}"#View Dashboard Log
kubectl logs -n kubernetes-dashboard deployment/kubernetes-dashboard -f#Check Dashboard Service
kubectl describe svc kubernetes-dashboard -n kubernetes-dashboard#Uninstall Dashboard
#Delete Dashboard
kubectl delete -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.7.0/aio/deploy/recommended.yaml#Delete Admin User
kubectl delete -f dashboard-admin.yml#Delete Namespace
kubectl delete namespace kubernetes-dashboard#Penutup
Pada episode 28 ini, kita telah membahas Kubernetes Dashboard secara mendalam. Kita sudah belajar cara install Dashboard v2.7.0, create admin user, access dashboard securely, dan manage cluster resource melalui web interface.
Key takeaway:
- Dashboard menyediakan web-based UI untuk Kubernetes management
- Install dengan single
kubectl applycommand - Require authentication via token atau kubeconfig
- Create ServiceAccount dengan appropriate RBAC permission
- Access via port-forward, NodePort, atau Ingress
- cluster-admin role give full access (use carefully)
- view role provide read-only access
- edit role allow modification tanpa delete
- Create long-lived token menggunakan Secret
- Gunakan namespace-specific role untuk limited access
- Selalu gunakan TLS untuk production deployment
- Implement Network Policy untuk restrict access
- Set resource limit pada Dashboard pod
- Monitor Dashboard access dan usage
- Consider alternative seperti Lens, K9s, Octant
- Keep Dashboard updated ke latest version
Kubernetes Dashboard make cluster management accessible melalui intuitive web interface. Dengan memahami Dashboard installation dan security best practice, kalian bisa provide team dengan visual cluster management sambil maintaining proper access control.
Bagaimana, makin jelas kan tentang Kubernetes Dashboard? Jadi, pastikan tetap semangat belajar dan nantikan episode selanjutnya!