
Belajar Kubernetes - Pengenalan dan Penjelasan RBAC dan RoleBinding
Di episode ini kita akan coba bahas Kubernetes RBAC (Role-Based Access Control) dan RoleBinding untuk authorization. Kita akan mempelajari Role, ClusterRole, RoleBinding, ClusterRoleBinding, dan best practice untuk implementing fine-grained access control.

#Pendahuluan
Di episode sebelumnya kita sudah belajar tentang ServiceAccount yang provide identity untuk Pod. Selanjutnya di episode 33 kali ini, kita akan coba bahas RBAC (Role-Based Access Control) dan RoleBinding, yang control apa yang authenticated user dan ServiceAccount bisa lakukan di cluster.
Catatan: Disini saya akan menggunakan Kubernetes Cluster yang di install melalui K3s.
Authentication answer "siapa kalian?" (ServiceAccount), sementara authorization answer "apa yang bisa kalian lakukan?" (RBAC). RBAC enable fine-grained access control, allowing kalian untuk grant specific permission ke user dan application based on principle of least privilege.
#Apa Itu RBAC?
RBAC (Role-Based Access Control) adalah Kubernetes authorization mechanism yang regulate access ke cluster resource based on role assigned ke user atau ServiceAccount.
Bayangkan RBAC seperti building security - badge kalian (ServiceAccount) identify kalian, tapi RBAC determine floor mana yang bisa kalian access, pintu mana yang bisa kalian buka, dan action apa yang bisa kalian perform di setiap room.
Key RBAC component:
- Role - Define permission dalam namespace
- ClusterRole - Define permission cluster-wide
- RoleBinding - Grant Role permission ke subject di namespace
- ClusterRoleBinding - Grant ClusterRole permission cluster-wide
- Subject - User, Group, atau ServiceAccount receiving permission
- Resource - Kubernetes object (pod, service, etc.)
- Verb - Action yang bisa performed (get, list, create, etc.)
#RBAC Component
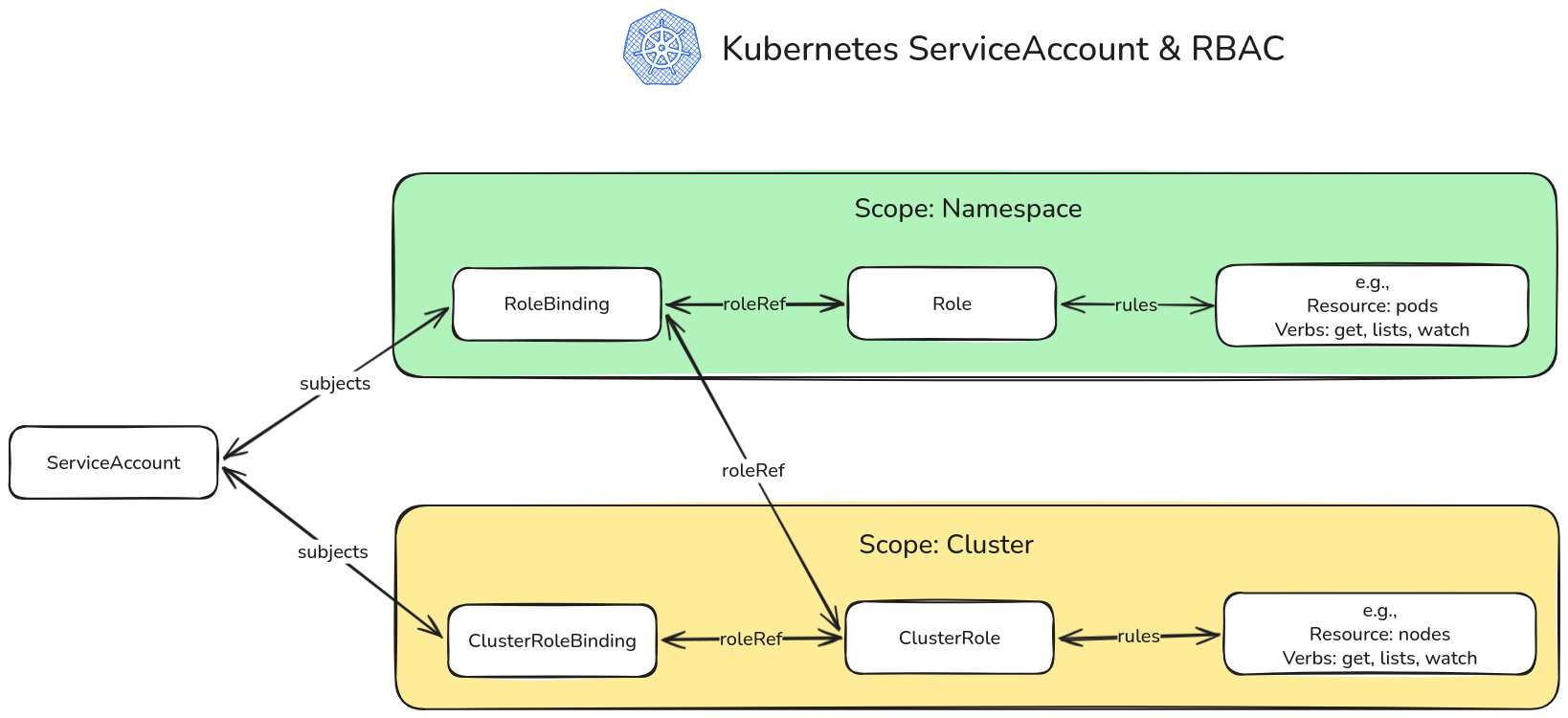 RBAC Illustration
RBAC Illustration#Role
Role define permission dalam specific namespace.
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: pod-reader
namespace: default
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]Karakteristik:
- Namespace-scoped
- Define apa yang bisa done
- Tidak grant permission by itself
- Need RoleBinding untuk take effect
#ClusterRole
ClusterRole define permission cluster-wide atau untuk cluster-scoped resource.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: node-reader
rules:
- apiGroups: [""]
resources: ["nodes"]
verbs: ["get", "list", "watch"]Karakteristik:
- Cluster-wide scope
- Bisa access cluster-scoped resource (node, namespace)
- Bisa bound di specific namespace via RoleBinding
- Bisa bound cluster-wide via ClusterRoleBinding
#RoleBinding
RoleBinding grant Role permission ke subject dalam namespace.
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: read-pods
namespace: default
subjects:
- kind: ServiceAccount
name: my-app-sa
namespace: default
roleRef:
kind: Role
name: pod-reader
apiGroup: rbac.authorization.k8s.ioKarakteristik:
- Namespace-scoped
- Bind Role atau ClusterRole ke subject
- Subject harus di same namespace (untuk ServiceAccount)
- Bisa reference ClusterRole untuk namespace-scoped access
#ClusterRoleBinding
ClusterRoleBinding grant ClusterRole permission cluster-wide.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: read-nodes
subjects:
- kind: ServiceAccount
name: monitoring-sa
namespace: monitoring
roleRef:
kind: ClusterRole
name: node-reader
apiGroup: rbac.authorization.k8s.ioKarakteristik:
- Cluster-wide scope
- Bind ClusterRole ke subject
- Grant access across semua namespace
- Gunakan carefully - powerful permission
#RBAC Rule
#API Group
Kubernetes resource belong ke API group:
rules:
# Core API group (empty string)
- apiGroups: [""]
resources: ["pods", "services", "configmaps"]
# apps API group
- apiGroups: ["apps"]
resources: ["deployments", "statefulsets"]
# rbac.authorization.k8s.io API group
- apiGroups: ["rbac.authorization.k8s.io"]
resources: ["roles", "rolebindings"]#Resource
Kubernetes object yang bisa accessed:
resources:
- "pods"
- "services"
- "deployments"
- "configmaps"
- "secrets"
- "persistentvolumeclaims"#Resource Name
Restrict access ke specific resource instance:
rules:
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["app-config", "app-secrets"]
verbs: ["get", "update"]#Verb
Action yang bisa performed:
verbs:
- "get" # Read single resource
- "list" # List resource
- "watch" # Watch untuk change
- "create" # Create new resource
- "update" # Update existing resource
- "patch" # Partially update resource
- "delete" # Delete resource
- "deletecollection" # Delete multiple resource#Subresource
Access ke resource subresource:
rules:
- apiGroups: [""]
resources: ["pods/log"]
verbs: ["get"]
- apiGroups: [""]
resources: ["pods/exec"]
verbs: ["create"]#Membuat RBAC Resource
#Contoh 1: Read-Only Access ke Pod
# Role
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: pod-reader
namespace: production
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]
---
# RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: read-pods
namespace: production
subjects:
- kind: ServiceAccount
name: app-reader
namespace: production
roleRef:
kind: Role
name: pod-reader
apiGroup: rbac.authorization.k8s.io#Contoh 2: Full Access ke Deployment
# Role
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: deployment-admin
namespace: development
rules:
- apiGroups: ["apps"]
resources: ["deployments"]
verbs: ["get", "list", "watch", "create", "update", "patch", "delete"]
---
# RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: deployment-admin-binding
namespace: development
subjects:
- kind: ServiceAccount
name: deployer-sa
namespace: development
roleRef:
kind: Role
name: deployment-admin
apiGroup: rbac.authorization.k8s.io#Contoh 3: Cluster-Wide Read Access
# ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: cluster-reader
rules:
- apiGroups: [""]
resources: ["pods", "services", "nodes"]
verbs: ["get", "list", "watch"]
- apiGroups: ["apps"]
resources: ["deployments", "statefulsets"]
verbs: ["get", "list", "watch"]
---
# ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: cluster-reader-binding
subjects:
- kind: ServiceAccount
name: monitoring-sa
namespace: monitoring
roleRef:
kind: ClusterRole
name: cluster-reader
apiGroup: rbac.authorization.k8s.io#Contoh 4: Multiple Resource dan Verb
# Role
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: app-manager
namespace: production
rules:
# Manage Deployment
- apiGroups: ["apps"]
resources: ["deployments", "replicasets"]
verbs: ["get", "list", "watch", "create", "update", "patch", "delete"]
# Manage Service
- apiGroups: [""]
resources: ["services"]
verbs: ["get", "list", "watch", "create", "update", "patch", "delete"]
# Read ConfigMap dan Secret
- apiGroups: [""]
resources: ["configmaps", "secrets"]
verbs: ["get", "list"]
# View Pod dan log
- apiGroups: [""]
resources: ["pods", "pods/log"]
verbs: ["get", "list", "watch"]
---
# RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: app-manager-binding
namespace: production
subjects:
- kind: ServiceAccount
name: app-manager-sa
namespace: production
roleRef:
kind: Role
name: app-manager
apiGroup: rbac.authorization.k8s.io#Built-in ClusterRole
Kubernetes provide default ClusterRole:
#view
Read-only access ke most resource:
kubectl get clusterrole view -o yamlPermission:
- Read pod, service, deployment, etc.
- Tidak bisa read secret
- Tidak bisa modify resource
#edit
Read-write access ke most resource:
kubectl get clusterrole edit -o yamlPermission:
- Semua view permission
- Create, update, delete resource
- Tidak bisa modify role atau rolebinding
#admin
Full access dalam namespace:
kubectl get clusterrole admin -o yamlPermission:
- Semua edit permission
- Manage role dan rolebinding
- Tidak bisa modify namespace itself
#cluster-admin
Full cluster access:
kubectl get clusterrole cluster-admin -o yamlPermission:
- Unrestricted access ke semua resource
- Bisa perform any action
- Gunakan dengan extreme caution
#Menggunakan Built-in Role
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: developer-view
namespace: development
subjects:
- kind: ServiceAccount
name: developer-sa
namespace: development
roleRef:
kind: ClusterRole
name: view # Built-in ClusterRole
apiGroup: rbac.authorization.k8s.io#Aggregated ClusterRole
Combine multiple ClusterRole:
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: monitoring-role
aggregationRule:
clusterRoleSelectors:
- matchLabels:
rbac.example.com/aggregate-to-monitoring: "true"
rules: [] # Rule automatically filled by aggregation
---
# Component role 1
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: monitoring-pods
labels:
rbac.example.com/aggregate-to-monitoring: "true"
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]
---
# Component role 2
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: monitoring-nodes
labels:
rbac.example.com/aggregate-to-monitoring: "true"
rules:
- apiGroups: [""]
resources: ["nodes"]
verbs: ["get", "list", "watch"]#Testing RBAC
#Check Permission
# Check jika kalian bisa perform action
kubectl auth can-i create deployments
# Check untuk specific user/ServiceAccount
kubectl auth can-i get pods --as=system:serviceaccount:default:my-app-sa
# Check di specific namespace
kubectl auth can-i delete services --namespace=production
# List semua permission
kubectl auth can-i --list
kubectl auth can-i --list --as=system:serviceaccount:default:my-app-sa#Impersonate User
# Run command as ServiceAccount
kubectl get pods --as=system:serviceaccount:default:my-app-sa
# Run command as user
kubectl get pods --as=john@example.com#Contoh Praktis
#Contoh 1: CI/CD Pipeline ServiceAccount
# ServiceAccount
apiVersion: v1
kind: ServiceAccount
metadata:
name: cicd-deployer
namespace: default
---
# Role - Deploy application
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: deployer-role
namespace: production
rules:
# Manage Deployment
- apiGroups: ["apps"]
resources: ["deployments"]
verbs: ["get", "list", "create", "update", "patch"]
# Manage Service
- apiGroups: [""]
resources: ["services"]
verbs: ["get", "list", "create", "update", "patch"]
# Manage ConfigMap
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["get", "list", "create", "update", "patch"]
# Read Pod (untuk status checking)
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]
---
# RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: cicd-deployer-binding
namespace: production
subjects:
- kind: ServiceAccount
name: cicd-deployer
namespace: default
roleRef:
kind: Role
name: deployer-role
apiGroup: rbac.authorization.k8s.io#Contoh 2: Developer Access
# ServiceAccount
apiVersion: v1
kind: ServiceAccount
metadata:
name: developer
namespace: development
---
# Role - Development environment access
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: developer-role
namespace: development
rules:
# Full access ke Deployment
- apiGroups: ["apps"]
resources: ["deployments", "replicasets"]
verbs: ["*"]
# Full access ke Service
- apiGroups: [""]
resources: ["services"]
verbs: ["*"]
# Full access ke ConfigMap
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["*"]
# Read-only Secret
- apiGroups: [""]
resources: ["secrets"]
verbs: ["get", "list"]
# Pod management
- apiGroups: [""]
resources: ["pods", "pods/log", "pods/exec"]
verbs: ["get", "list", "watch", "create", "delete"]
---
# RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: developer-binding
namespace: development
subjects:
- kind: ServiceAccount
name: developer
namespace: development
roleRef:
kind: Role
name: developer-role
apiGroup: rbac.authorization.k8s.io#Contoh 3: Monitoring System
# ServiceAccount
apiVersion: v1
kind: ServiceAccount
metadata:
name: prometheus
namespace: monitoring
---
# ClusterRole - Read metric cluster-wide
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: prometheus-role
rules:
# Read node
- apiGroups: [""]
resources: ["nodes", "nodes/metrics", "nodes/stats"]
verbs: ["get", "list", "watch"]
# Read pod
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list", "watch"]
# Read service
- apiGroups: [""]
resources: ["services", "endpoints"]
verbs: ["get", "list", "watch"]
# Read metric
- apiGroups: ["metrics.k8s.io"]
resources: ["nodes", "pods"]
verbs: ["get", "list"]
---
# ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: prometheus-binding
subjects:
- kind: ServiceAccount
name: prometheus
namespace: monitoring
roleRef:
kind: ClusterRole
name: prometheus-role
apiGroup: rbac.authorization.k8s.io#Contoh 4: Namespace Admin
# ServiceAccount
apiVersion: v1
kind: ServiceAccount
metadata:
name: namespace-admin
namespace: production
---
# RoleBinding - Gunakan built-in admin role
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: namespace-admin-binding
namespace: production
subjects:
- kind: ServiceAccount
name: namespace-admin
namespace: production
roleRef:
kind: ClusterRole
name: admin # Built-in ClusterRole
apiGroup: rbac.authorization.k8s.io#Kesalahan Umum dan Pitfall
#Kesalahan 1: Granting cluster-admin
Problem: Giving cluster-admin ke everyone.
# Bad: Terlalu permissive
roleRef:
kind: ClusterRole
name: cluster-adminSolusi: Grant minimum necessary permission:
# Good: Specific permission
roleRef:
kind: ClusterRole
name: view#Kesalahan 2: Menggunakan ClusterRoleBinding untuk Namespace Access
Problem: Granting cluster-wide access ketika namespace access sufficient.
# Bad: Cluster-wide access
kind: ClusterRoleBindingSolusi: Gunakan RoleBinding untuk namespace-scoped access:
# Good: Namespace-scoped
kind: RoleBinding
metadata:
namespace: production#Kesalahan 3: Wildcard Permission
Problem: Menggunakan wildcard (*) untuk everything.
# Bad: Terlalu broad
rules:
- apiGroups: ["*"]
resources: ["*"]
verbs: ["*"]Solusi: Be specific:
# Good: Specific permission
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list"]#Kesalahan 4: Tidak Testing Permission
Problem: Deploying RBAC tanpa testing.
Solusi: Selalu test:
kubectl auth can-i get pods --as=system:serviceaccount:default:my-app-sa#Kesalahan 5: Lupa API Group
Problem: Wrong atau missing API group.
# Bad: Missing API group untuk deployment
rules:
- apiGroups: [""] # Wrong! Deployment ada di "apps"
resources: ["deployments"]Solusi: Gunakan correct API group:
# Good: Correct API group
rules:
- apiGroups: ["apps"]
resources: ["deployments"]#Best Practice
#Principle of Least Privilege
Grant hanya necessary permission:
# Minimal permission
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list"] # Hanya yang needed#Gunakan Namespace-Scoped Role
Prefer Role over ClusterRole:
# Good: Namespace-scoped
kind: Role
metadata:
namespace: production#Leverage Built-in Role
Gunakan view, edit, admin ketika appropriate:
roleRef:
kind: ClusterRole
name: view # Built-in role#Document RBAC Policy
metadata:
name: app-manager
annotations:
description: "Manage application di production namespace"
permissions: "deployments, services, configmaps"#Regular Audit
Review RBAC regularly:
# List semua RoleBinding
kubectl get rolebindings --all-namespaces
# List semua ClusterRoleBinding
kubectl get clusterrolebindings
# Check specific permission
kubectl auth can-i --list --as=system:serviceaccount:default:my-app-sa#Separate Role by Function
# Reader role
kind: Role
name: pod-reader
# Writer role
kind: Role
name: pod-writer
# Admin role
kind: Role
name: pod-admin#Melihat RBAC Resource
#Get Role
kubectl get roles
kubectl get roles --all-namespaces
kubectl get clusterroles#Get RoleBinding
kubectl get rolebindings
kubectl get rolebindings --all-namespaces
kubectl get clusterrolebindings#Describe RBAC Resource
kubectl describe role pod-reader
kubectl describe rolebinding read-pods
kubectl describe clusterrole view
kubectl describe clusterrolebinding cluster-admin#View RBAC YAML
kubectl get role pod-reader -o yaml
kubectl get rolebinding read-pods -o yaml#Menghapus RBAC Resource
# Delete Role
kubectl delete role pod-reader
# Delete RoleBinding
kubectl delete rolebinding read-pods
# Delete ClusterRole
kubectl delete clusterrole custom-role
# Delete ClusterRoleBinding
kubectl delete clusterrolebinding custom-binding#Penutup
Pada episode 33 ini, kita telah membahas RBAC dan RoleBinding di Kubernetes secara mendalam. Kita sudah belajar cara implement fine-grained access control menggunakan Role, ClusterRole, RoleBinding, dan ClusterRoleBinding.
Key takeaway:
- RBAC control apa yang authenticated subject bisa lakukan
- Role define namespace-scoped permission
- ClusterRole define cluster-wide permission
- RoleBinding grant Role ke subject di namespace
- ClusterRoleBinding grant ClusterRole cluster-wide
- Rule specify apiGroup, resource, dan verb
- Verb include get, list, watch, create, update, delete
- Built-in role: view, edit, admin, cluster-admin
- Gunakan principle of least privilege
- Prefer Role over ClusterRole ketika possible
- Test permission dengan kubectl auth can-i
- Document RBAC policy
- Regular audit permission
- Avoid cluster-admin kecuali necessary
- Separate role by function
RBAC fundamental untuk Kubernetes security. Dengan memahami dan properly implementing RBAC, kalian bisa ensure secure, controlled access ke cluster resource, protecting application dan data dari unauthorized access.
Bagaimana, makin jelas kan tentang RBAC dan RoleBinding di Kubernetes? Jadi, pastikan tetap semangat belajar dan nantikan episode selanjutnya!