#Project Overview
NestJS Boilerplate is a powerful, type-safe starter template designed for building production-ready backend applications. It comes pre-configured with essential tools and best practices, allowing developers to focus on business logic rather than infrastructure setup.
The boilerplate emphasizes three core principles:
- Developer Experience - Fully typed, well-documented, and easy to extend
- Production Readiness - Security, observability, and performance built-in
- Scalability - Designed to grow from MVP to enterprise-scale applications
#Background & Motivation
This project was born from my experience building multiple backend applications and repeatedly setting up the same foundational features. I noticed that every new project required:
- Authentication and authorization setup
- Database configuration and migrations
- API documentation
- Logging and monitoring
- Error handling and validation
- Testing infrastructure
Instead of reinventing the wheel for each project, I decided to create a comprehensive boilerplate that includes all these essentials while following industry best practices.
The goal was to create a starting point that:
Reduces initial setup time from days to minutes, while maintaining flexibility for customization and ensuring production-grade quality from day one.
#Problem Statement
When starting a new backend project, developers face several challenges:
- Setting up authentication with secure token management
- Implementing proper authorization with role-based access control
- Configuring database ORM with type safety
- Establishing observability (logs, metrics, traces)
- Writing comprehensive API documentation
- Setting up testing infrastructure
- Implementing security best practices (CORS, rate limiting, etc.)
Each of these requires significant time and expertise. Without a solid foundation, projects often accumulate technical debt early on.
#Solution Approach
This boilerplate provides a complete solution with the following architecture:
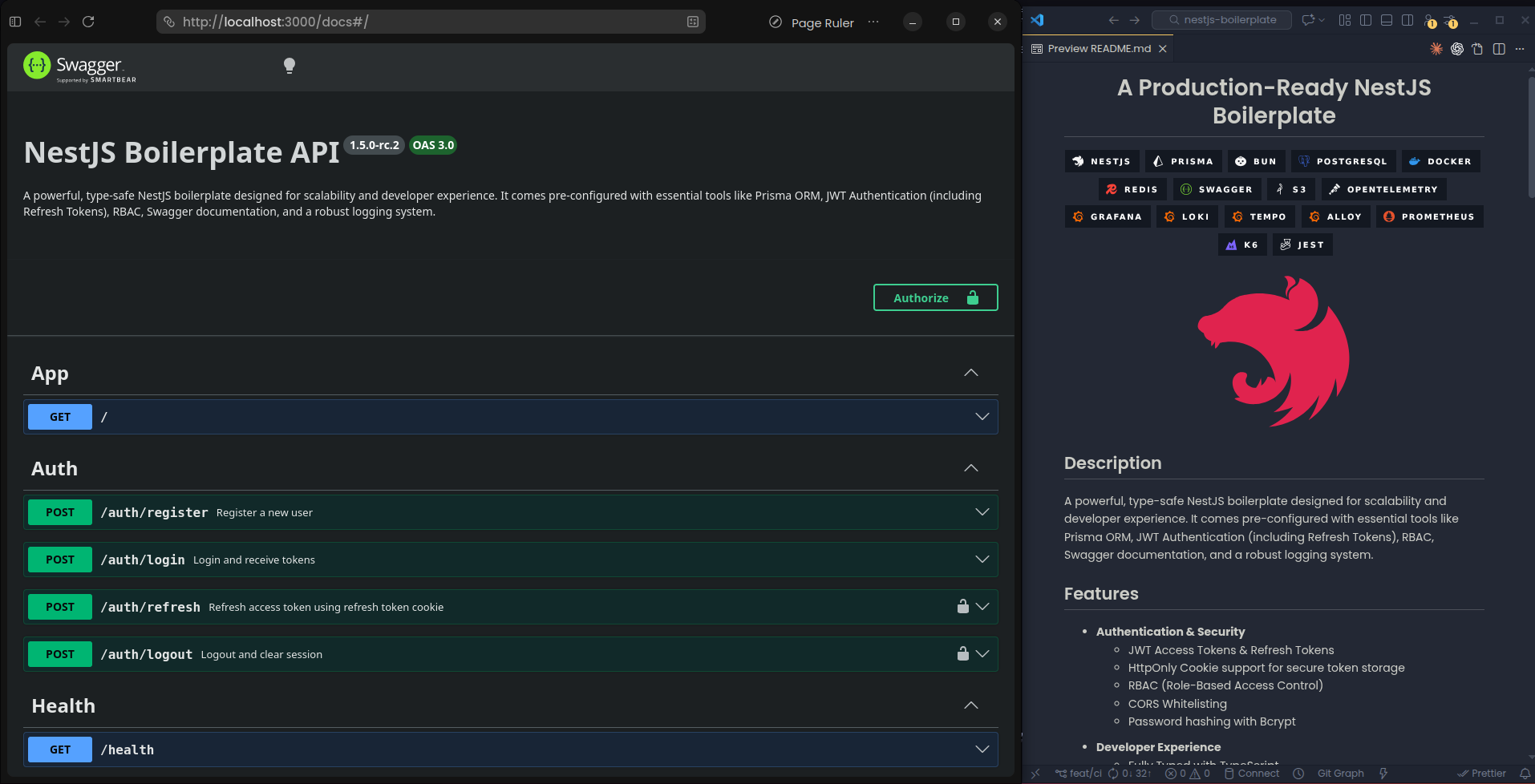
#1. Authentication & Security
- JWT-based authentication with access and refresh tokens
- HttpOnly cookies for secure token storage
- Role-Based Access Control (RBAC) for fine-grained permissions
- Password hashing with Bcrypt
- CORS whitelisting and rate limiting
#2. Database & ORM
- Prisma ORM for type-safe database access
- PostgreSQL as the primary database
- Migration system for schema versioning
- Seeding support for development data
#3. API Documentation
- OpenAPI (Swagger) integration at
/docs - Automatic schema generation from DTOs
- Interactive API testing interface
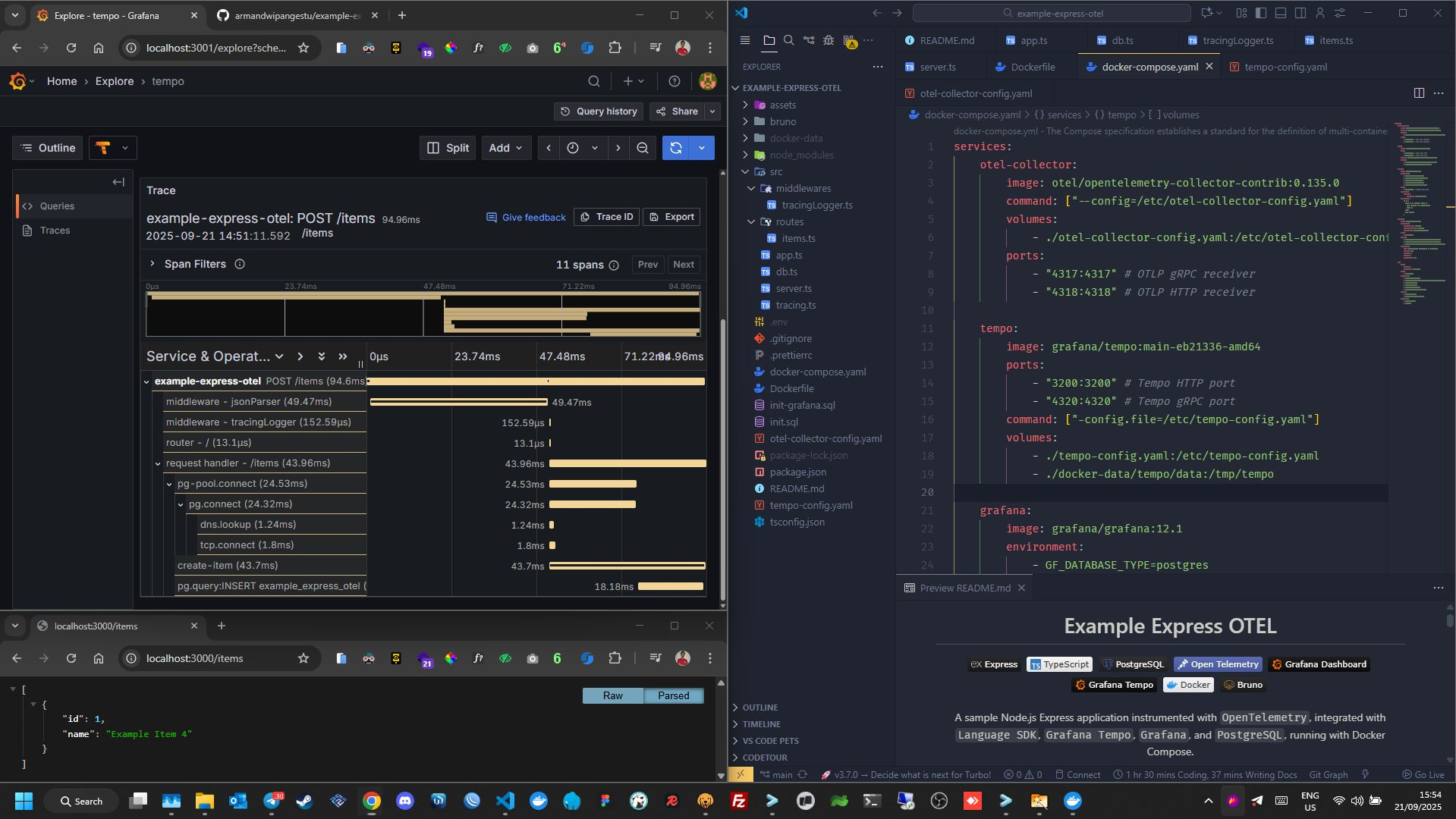
#4. Observability Stack
- Custom Winston logger with daily rotation
- OpenTelemetry for distributed tracing
- Prometheus metrics exporter at
/metrics(port 9464) - Integration with Grafana, Loki, Tempo, and Prometheus
- Log correlation with Trace ID injection
#5. Developer Experience
- Full TypeScript support with strict typing
- DTO validation using
class-validatorandclass-transformer - Global validation pipe and error handling
- Docker and Docker Compose for local development
- Powered by Bun for fast execution
#6. Testing & Quality
- Jest for unit and E2E testing
- k6 for load testing
- CI/CD with GitHub Actions
- Semantic versioning and conventional commits
#Technical Highlights
#Authentication Flow
The boilerplate implements a secure authentication flow:
- User logs in with credentials
- Server generates access token (short-lived) and refresh token (long-lived)
- Tokens are stored in HttpOnly cookies
- Access token is used for API requests
- When access token expires, refresh token is used to obtain a new one
- Refresh token rotation for enhanced security
#Observability Architecture
The observability stack provides complete visibility into application behavior:
- Logs - Structured logging with Winston, shipped to Loki via Alloy
- Metrics - Application and system metrics exposed for Prometheus
- Traces - Distributed tracing with OpenTelemetry, stored in Tempo
- Dashboards - Pre-configured Grafana dashboards for metrics and logs
#RBAC Implementation
Role-Based Access Control is implemented using:
- Decorators for route-level permissions
- Guards for authorization checks
- Flexible role hierarchy
- Easy to extend with custom roles and permissions
#What I Learned
Building this boilerplate deepened my understanding of:
- NestJS architecture and best practices
- Secure authentication patterns with JWT
- Type-safe database access with Prisma
- Observability implementation in Node.js applications
- Testing strategies for backend applications
- Docker containerization and orchestration
- Performance optimization techniques
The project also taught me the importance of:
- Documentation - Good docs make adoption easier
- Flexibility - Boilerplates should be opinionated but not rigid
- Maintenance - Keeping dependencies updated and secure
- Community - Open source collaboration and feedback
#Why This Project Matters
This boilerplate solves a real problem for backend developers:
- Reduces project setup time significantly
- Ensures security best practices from the start
- Provides production-ready observability
- Includes comprehensive testing infrastructure
- Follows industry standards and conventions
It's not just a template - it's a learning resource that demonstrates how to build scalable, maintainable backend applications.
#Conclusion
NestJS Boilerplate represents my commitment to building high-quality, production-ready backend applications. It combines security, observability, and developer experience into a single, well-documented package.
Whether you're building an MVP or an enterprise application, this boilerplate provides a solid foundation to build upon.